Apr 20 2026
/
What Is a Network Access Controller (NAC) and Why Does Your Business Need One?
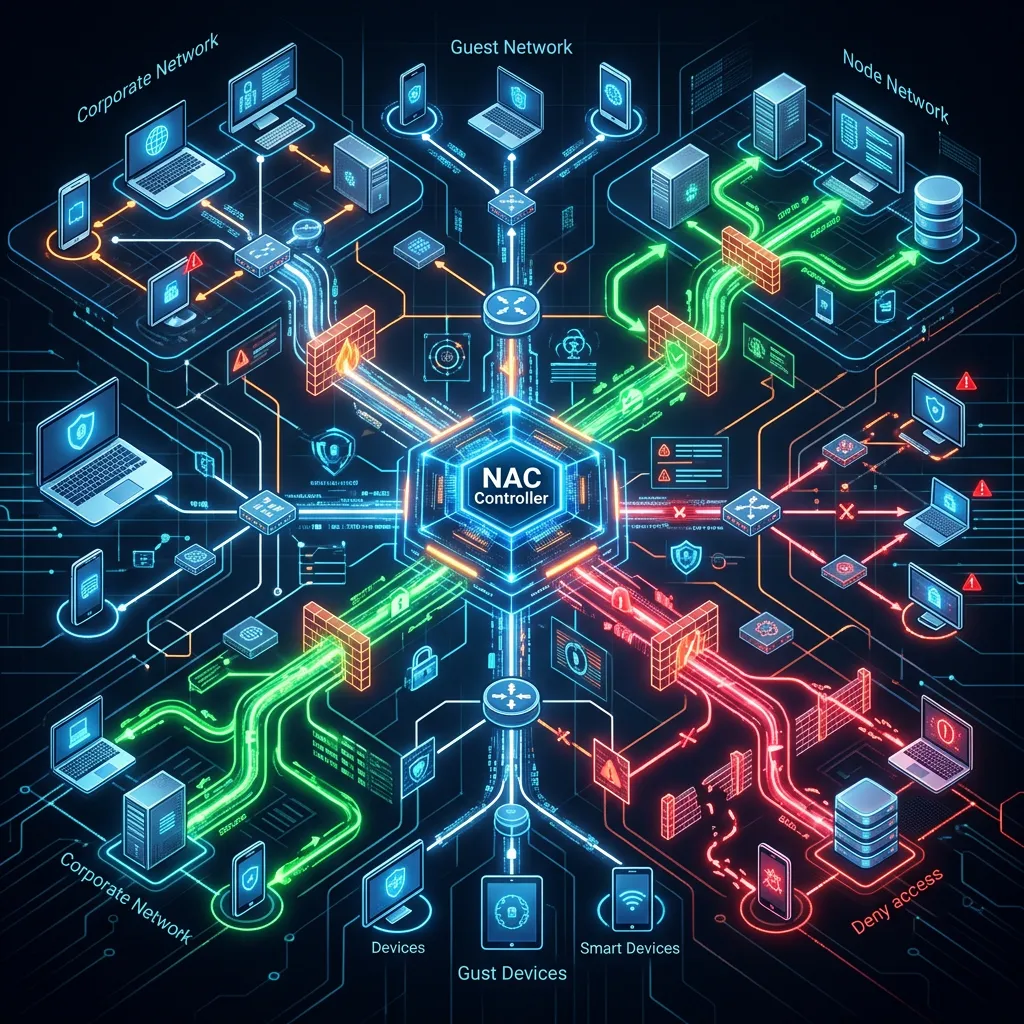
A Network Access Controller (NAC) is a security solution that manages and restricts network access based on predefined policies. It authenticates users, checks device compliance, and prevents unauthorized access. Your business needs a NAC to protect sensitive data, mitigate cyber threats, and ensure only secure devices connect to your infrastructure.
Maintaining a secure IT environment requires absolute visibility and control over every device attempting to connect to your corporate network. As organizations expand their digital footprints, the perimeter of traditional networks has evolved, bringing new vulnerabilities. Implementing strict access policies is no longer an optional security measure but a fundamental requirement for operational resilience.
A Network Access Controller serves as the ultimate gatekeeper for your IT infrastructure. By enforcing stringent security protocols before allowing any device to communicate with your internal systems, a NAC minimizes the risk of unauthorized access. This proactive approach to network security helps organizations maintain seamless operations while safeguarding critical assets from external and internal threats.
Understanding the mechanics and benefits of a NAC allows business leaders and IT professionals to make informed decisions regarding their cybersecurity posture. By integrating advanced access control mechanisms, enterprises can foster a secure, reliable, and compliant digital environment.
Understanding the Core Functions of a Network Access Controller
A comprehensive NAC solution operates through multiple layers of verification and policy enforcement. Its primary objective is to evaluate every connection request and determine the appropriate level of access based on organizational security guidelines.
Authentication and Authorization
The fundamental mechanism of a NAC involves verifying the identity of the user and the device. Authentication ensures that the entity requesting access is legitimate, often utilizing protocols such as 802.1X, Active Directory integration, or multi-factor authentication (MFA). Once authenticated, the authorization phase determines the specific network resources the user is permitted to access. This principle of least privilege ensures that individuals only interact with the data and applications necessary for their specific roles, thereby limiting potential internal vulnerabilities.
Device Compliance and Profiling
Beyond user identity, a NAC evaluates the security posture of the device itself. Device profiling involves scanning the endpoint to ensure it meets the organization’s security standards. The controller checks for active antivirus software, updated operating systems, and the absence of known vulnerabilities. If a device fails to meet these compliance requirements, the NAC can quarantine the endpoint, restrict its access to a remediation network, or block the connection entirely until the necessary security updates are applied.
The Imperative for NAC in Modern Enterprises
Securing the enterprise network requires solutions capable of adapting to complex and dynamic environments. A Network Access Controller provides the necessary oversight to manage diverse connection requests safely.
Mitigating Advanced Cyber Threats
Cyber adversaries continuously develop sophisticated methods to infiltrate corporate networks. A single compromised device can serve as a gateway for malware, ransomware, or unauthorized data extraction. A NAC drastically reduces this risk by halting non-compliant or unrecognized devices at the network edge. By isolating potential threats before they can establish a foothold, organizations protect their operational integrity and secure their confidential information. Explore Magnus Gulf’s cybersecurity solutions to learn how the right tools can help defend your network perimeter.
Managing the Proliferation of IoT Devices
The integration of Internet of Things (IoT) devices introduces a significant challenge for network administrators. Printers, smart thermostats, and security cameras often lack robust built-in security features, making them attractive targets for exploitation. A NAC systematically identifies and profiles these headless devices, assigning them to segmented networks with restricted access. This segmentation ensures that even if an IoT device is compromised, the attacker cannot pivot to the core corporate network.
Why Choose Magnus Infotech for Your IT Distribution Needs
Implementing robust security infrastructure requires a reliable technology partner. Welcome to Magnus Infotech, your trusted IT distribution partner dedicated to delivering seamless technology solutions. We operate as an authorized distributor of the world’s leading technology products, headquartered in the Al Tawhidi Building on Al Mankhool Street in Dubai, UAE.
Magnus Gulf acts as a premier B2B IT distribution company, proudly serving as the bridge between global tech vendors and regional resellers or system integrators across the Middle East. Our unwavering commitment is to provide you with an exceptional experience by delivering unparalleled solutions marked by a seamless blend of quality and value. With a commitment to excellence, we specialize in providing cutting-edge products in the domains of Networking & Wireless, Security Surveillance, Unified Communication, and Server & Storage.
The extensive network of our channel partners is a testament to our dedication in fostering mutually beneficial relationships and ensuring that your business receives the highly secure, reliable technology solutions it deserves.
Securing Your Enterprise Network for the Future
Network security is an ongoing commitment to protecting your organizational assets, data, and personnel. Integrating a Network Access Controller establishes a highly secure, controlled environment where every connection is verified, authenticated, and authorized. By proactively managing network access, your business can operate with confidence, knowing that your infrastructure is defended by advanced, policy-driven security measures.
Frequently Asked Questions
1. How does a NAC differ from a traditional firewall?
While a firewall monitors and controls incoming and outgoing traffic based on predetermined security rules, a NAC focuses specifically on the endpoints connecting to the internal network. A NAC evaluates the identity and security posture of the device and user before granting internal access, acting as an internal gatekeeper rather than a perimeter defense.
2. Can a NAC solution manage Internet of Things (IoT) devices?
Yes. A robust NAC solution excels at profiling and authenticating IoT devices. Because IoT endpoints typically cannot authenticate via traditional methods like username and password, a NAC identifies them based on MAC addresses or behavioral profiles and segments them into restricted network areas to maintain overall security.
3. Is a Network Access Controller difficult to deploy?
Deployment complexity depends on the size of the network and the specific access policies required. However, partnering with experienced technology distributors and system integrators ensures a structured deployment. Proper planning, phased rollouts, and comprehensive policy definitions facilitate a smooth integration with existing IT infrastructure.
4. How does NAC assist with regulatory compliance?
Many industry regulations, such as HIPAA, PCI-DSS, and GDPR, require strict access controls and continuous monitoring of network activity. A NAC provides automated policy enforcement, detailed access logs, and compliance reporting, making it significantly easier for organizations to demonstrate adherence to legal and regulatory security frameworks.
5. What happens if a device fails the NAC compliance check?
If an endpoint does not meet the organization’s security criteria—such as having outdated antivirus definitions or unpatched operating systems—the NAC will deny standard network access. The device is typically placed in a restricted remediation VLAN where it can download necessary updates to become compliant before being granted full access.
