Apr 20 2026
/
What Is Network Segmentation and Why It Matters for Enterprise Security?
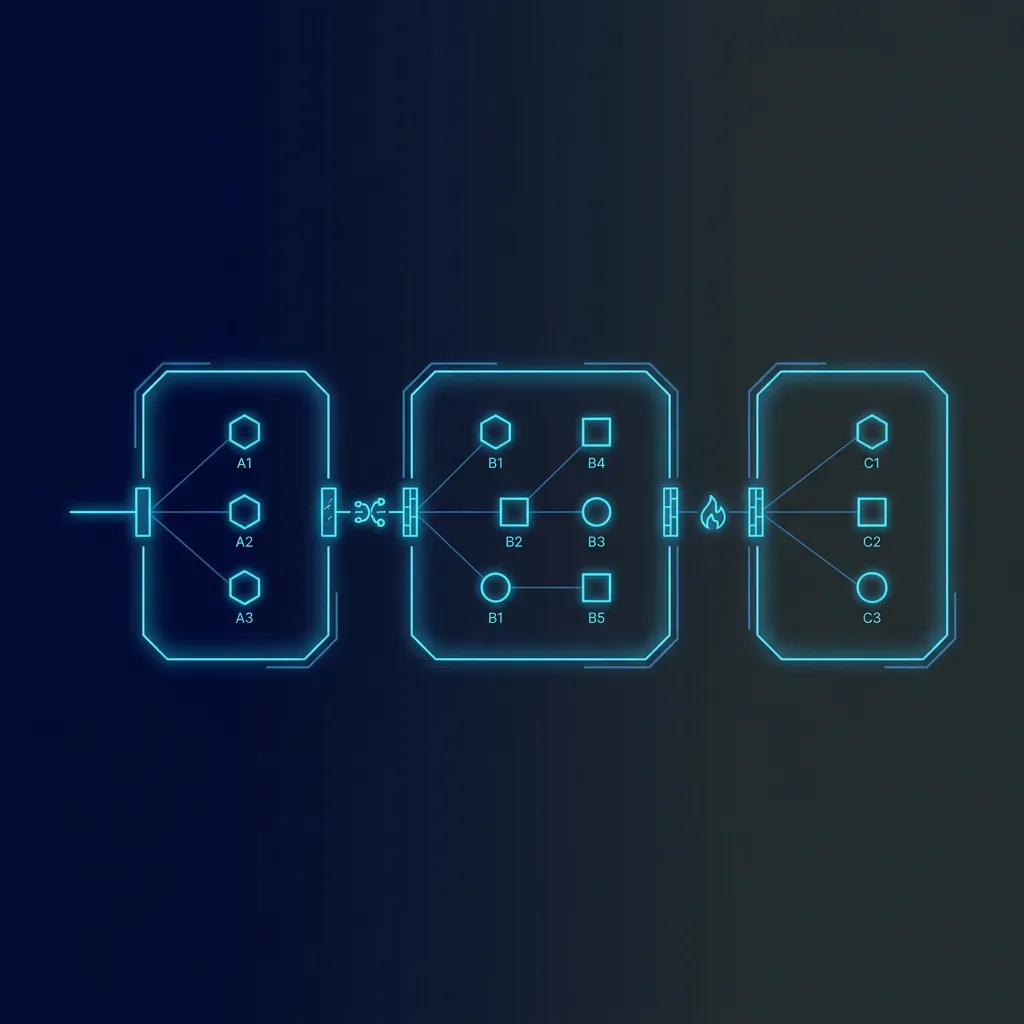
Network segmentation is the strategic practice of dividing a broad corporate network into smaller, isolated sub-networks. This approach significantly enhances enterprise security by containing potential breaches, limiting the lateral movement of attackers, and ensuring that sensitive data remains fully protected even if one specific segment is compromised.
Managing a large-scale corporate infrastructure requires immense diligence and foresight. As organizations scale, their internal systems become increasingly complex, expanding the attack surface available to malicious actors. When all digital assets share a single, unpartitioned space, a single vulnerability can compromise the entire infrastructure. This is why adopting advanced architectural strategies is critical for maintaining robust operational continuity.
By dividing a unified network into distinct, secure zones, IT administrators can establish precise access controls. This methodology ensures that users and applications only access the resources necessary for their specific functions. Consequently, it minimizes the risk of unauthorized access and simplifies the monitoring of internal traffic.
Understanding the mechanics and benefits of this security strategy is essential for modern businesses. This comprehensive guide explains the fundamental concepts of network segmentation, its profound impact on enterprise security, and how organizations can successfully implement these principles to safeguard their most valuable digital assets.
The Mechanics of Network Segmentation
Network segmentation operates on the principle of least privilege. Instead of granting users and devices broad access across the entire infrastructure, segmentation isolates traffic based on specific business needs, departments, or security clearance levels.
Physical vs. Logical Segmentation
Historically, administrators achieved segmentation through physical means, requiring separate routers, switches, and wiring for different departments. While highly secure, this physical approach is often costly and difficult to scale.
Modern enterprises rely on logical segmentation. Using Virtual Local Area Networks (VLANs), Software-Defined Networking (SDN), and next-generation firewalls, organizations can create isolated environments on the same physical hardware. This allows for immense flexibility. IT teams can adjust security policies, create new segments, and monitor traffic flows through centralized software interfaces, ensuring a highly responsive and scalable security posture. Explore our networking and wireless solutions to find the right hardware for logical segmentation deployments.
Key Benefits for Enterprise Security
Implementing a segmented architecture provides an array of strategic advantages that directly fortify an organization’s defense mechanisms.
Containing Cyber Threats
When a cyberattack occurs in a flat network, the malicious software can easily spread from a low-level workstation to critical data servers. Segmentation acts as a series of digital bulkheads. If ransomware infects a device in the marketing department’s segment, firewalls and strict access control lists prevent that infection from moving into the financial or human resources databases. This containment drastically reduces the overall damage and operational downtime associated with an attack. Learn how our cybersecurity solutions can help build these protective layers across your enterprise.
Improved Performance and Monitoring
Beyond security, segmentation greatly enhances overall system performance. By confining local traffic to its specific segment, administrators reduce unnecessary congestion across the broader infrastructure. Furthermore, monitoring tools can focus on the specific traffic patterns of individual segments. This granularity allows security teams to identify anomalies and suspicious behavior much faster than they could within a chaotic, unsegmented environment.
Flat Network vs. Segmented Network Comparison
To clearly illustrate the operational differences, review the following comparison table:
| Architectural Feature | Flat Network Design | Segmented Network Design |
|---|---|---|
| Security Posture | Highly vulnerable to widespread breaches | Highly resilient and controlled |
| Lateral Movement | Unrestricted access across devices | Strictly blocked by internal firewalls |
| Access Control | Broad and generalized permissions | Granular, role-based access |
| Traffic Congestion | High, as all data shares one pathway | Low, as traffic is localized |
| Regulatory Compliance | Extremely difficult to audit effectively | Streamlined and isolated auditing |
Implementation Strategies and Best Practices
Transitioning to a segmented architecture requires careful planning and a deep understanding of organizational workflows.
Mapping the Digital Environment
The first critical step involves conducting a comprehensive inventory of all digital assets. Administrators must identify sensitive data repositories, categorize user roles, and understand the communication requirements between different applications. Without this foundational knowledge, administrators risk creating segments that disrupt legitimate business operations.
Establishing Security Policies
Once the assets are mapped, the organization must define stringent security policies for each segment. This involves configuring access control lists and deploying internal firewalls to govern the flow of information between zones. It is vital to adopt a “zero trust” mindset, meaning that no traffic is trusted by default, regardless of whether it originates from inside or outside the corporate perimeter. Our cybersecurity solutions portfolio includes the advanced firewall and security products needed to enforce these policies effectively.
Phased Deployment Chart
Successful implementation rarely happens overnight. Below is a chart representing the typical phases of a structured deployment:
[ Phase 1: Discovery & Asset Mapping ]
██████████ (20% of project time)
- Identify critical assets and traffic flows.
[ Phase 2: Design & Policy Creation ]
███████████████ (30% of project time)
- Define access controls and zero-trust policies.
[ Phase 3: Pilot Implementation ]
█████ (10% of project time)
- Test segmentation on non-critical departments.
[ Phase 4: Full Deployment ]
████████████████████ (40% of project time)
- Roll out logical segments across the enterprise.
[ Phase 5: Continuous Monitoring ]
█████████████████████████ (Ongoing)
- Analyze traffic, audit logs, and refine policies.Why Choose Magnus Infotech for Your IT Distribution Needs
As enterprises across the Middle East look to fortify their infrastructures with advanced security protocols like network segmentation, having a reliable technology partner is paramount.
Welcome to Magnus, your trusted IT distribution partner dedicated to delivering seamless technology solutions. Operating as a premier B2B IT distribution company headquartered in Dubai, UAE (located at the Al Tawhidi Building, Al Mankhool Street), Magnus Gulf acts as the definitive bridge between global technology vendors and regional resellers.
Our unwavering commitment is to provide you with an exceptional experience. We specialize in providing cutting-edge products and solutions in the domains of Networking & Wireless, Security Surveillance, Unified Communication, and Server & Storage. When system integrators require reliable, top-tier hardware and software to deploy complex network segmentations, they turn to Magnus. The extensive network of our channel partners is a testament to the dedication in fostering mutually beneficial relationships, ensuring that your business receives the high-performance technology solutions it deserves.
Partner with Magnus Infotech today to secure the innovative technology required to build resilient, segmented, and future-proof corporate networks.
Frequently Asked Questions
1. What is the main purpose of network segmentation?
The primary purpose is to enhance security and performance by dividing a large network into smaller, manageable sub-networks. This division isolates sensitive data and prevents unauthorized users or malware from moving freely across the entire enterprise infrastructure.
2. How does logical segmentation differ from physical segmentation?
Physical segmentation requires separate hardware—like distinct routers and cables—for each network segment. Logical segmentation uses software configurations, such as VLANs and firewalls, to create secure, isolated zones on shared physical hardware, making it far more scalable and cost-effective. Browse our networking hardware to find enterprise-grade switches and routers suited for both approaches.
3. Will implementing network segmentation disrupt our current business operations?
If executed properly through a phased approach, disruptions are minimal. Administrators must carefully map existing traffic flows and application dependencies during the design phase to ensure that legitimate business communications remain open while unauthorized access is blocked. Contact us to consult with our team on a smooth, phased deployment plan.
4. Is network segmentation required for regulatory compliance?
While not explicitly mandated by every regulation, it is highly recommended and often necessary to meet strict frameworks like PCI-DSS or HIPAA. Segmentation allows organizations to isolate regulated data into specific zones, making it much easier to secure, monitor, and audit during compliance checks. Our cybersecurity solutions are designed to support compliance-ready enterprise environments.
5. What role does a "zero trust" architecture play in segmentation?
Zero trust and network segmentation work hand-in-hand. Zero trust dictates that no user or device is trusted by default, regardless of their location on the network. Segmentation provides the necessary architectural boundaries to enforce these strict verification policies at every internal checkpoint. Request support from our specialists to design a zero-trust segmentation strategy for your organization.
